Table of Contents
ToggleIntroduction
Here is a brief introduction to the Cyber security course fee. Cybersecurity is essential because it protects all categories of data from theft and damage. This includes sensitive data, personally identifiable information (PII), protected health information (PHI), personal information, intellectual property, data, and governmental and industry information systems.
What is Cyber Security?

What is Cyber Security, and how much does the Cyber Security Course Fee come to mind whenever you hear about this course. Cyber security protects an organization and its employees and assets against cyber threats. As cyberattacks become more common and sophisticated and corporate networks grow more complex, various cyber security solutions are required to mitigate corporate cyber risk.
Why is Cybersecurity Important?
Before you know about the cyber security course fee, you must first know the importance of cyber security. In today’s connected world, everyone benefits from advanced cyber defense programs. At an individual level, a cybersecurity attack can result in everything from identity theft to extortion attempts to the loss of essential data like family photos. Everyone relies on critical infrastructure like power plants, hospitals, and financial service companies. Securing these and other organizations is essential to keeping our society functioning.
The Types of Cybersecurity Threats

You should know the types of Cyber Security threats before going through the Cyber Security Course fees. Cybersecurity can be divided into the following types:
Phishing
Phishing is sending fraudulent emails that resemble emails from reputable sources. The aim is to steal sensitive data like credit card numbers and login information. It’s the most common type of cyber attack. You can help protect yourself through education or a technology solution that filters malicious emails.
Ransomware
Ransomware is a type of malicious software. Cyber Security Course fee, It is designed to extort money by blocking access to files or the computer system until the ransom is paid. Paying the ransom does not guarantee that the files will be recovered or the system restored.
Malware
Malware (short for “malicious software”) is a file or coding, typically delivered over a network, that infects, explores, steals or conducts virtually any behavior an attacker wants. And because malware comes in so many variants, numerous methods exist to infect computer systems.
Social Engineering
Social engineering is a tactic that adversaries use to trick you into revealing sensitive information. They can solicit a monetary payment or gain access to your confidential data. Social engineering can be combined with any of the threats listed above to make you more likely to click on links, download malware, or trust a malicious source.
What are the benefits of cybersecurity?

The benefits of implementing and maintaining cybersecurity practices include:
- Business protection against cyberattacks and data breaches.
- Protection for data and networks.
- Prevention of unauthorized user access.
- Improved recovery time after a breach.
- Protection for end users and endpoint devices.
- Regulatory compliance.
- Business continuity
The Disciplines of Cybersecurity

Cybersecurity is a broad field covering several disciplines. It can be divided into some pillars. You should know this before going through the Cyber Security Course fees.
Network Security
Most attacks occur over the network, and network security solutions are designed to identify and block these attacks. These solutions include data and access controls such as Data Loss Prevention (DLP), IAM (Identity Access Management), NAC (Network Access Control), and NGFW (Next-Generation Firewall) application controls to enforce safe web use policies.
Cloud Security
As organizations increasingly adopt cloud computing, securing the cloud becomes a major priority. A cloud security strategy includes cyber security solutions, controls, policies, and services that help to protect an organization’s entire cloud deployment (applications, data, infrastructure, etc.) against attack.
Endpoint Security
The zero-trust security model prescribes creating micro-segments around data wherever possible. Endpoint security is one way to do that with a mobile workforce. With endpoint security, Cyber Security Course fee, companies can secure end-user devices such as desktops and laptops with data and network security controls, advanced threat prevention such as anti-phishing and Anti-ransomware and technologies that provide forensics, such as endpoint detection and response (EDR) solutions.
Mobile Security
Often overlooked, mobile devices such as tablets and smartphones have access to corporate data, exposing businesses to threats from malicious apps, zero-day, phishing, and IM (Instant Messaging) attacks. Mobile security prevents these attacks and secures operating systems and devices from rooting and jailbreaking. Including an MDM (Mobile Device Management) solution enables enterprises to ensure only compliant mobile devices can access corporate assets.
IoT Security
While using Internet of Things (IoT) devices certainly delivers productivity benefits, Cyber Security Course fee, it also exposes organisations to new cyber threats. Threat actors seek out vulnerable devices inadvertently connected to the Internet for nefarious uses, such as a pathway into a corporate network or another bot in a global bot network.
IoT security protects these devices by discovering and classifying the connected devices and using IPS as a virtual patch to prevent exploits against vulnerable IoT devices.
What are the top Cybersecurity Challenges?
Before you know about the cyber security course fee, you must first know the challenges of Cyber Security. Cybersecurity is continually challenged by hackers, data loss, privacy, risk management and changing cybersecurity strategies. The number of cyberattacks is expected to remain the same soon. Moreover, increased entry points for attacks, such as with the arrival of the internet of things (IoT), and the growing attac
k surface rise, the need to secure networks and devices.
Significant challenges that must be continuously addressed include evolving threats, the data deluge, cybersecurity awareness training, the workforce shortage and skills gap, and supply chain and third-party risks.
Skill Requirements for Cyber Security Course Fee
Cyber Security course fees require students to have the following skills and knowledge:
- Technical Skills:
Technical skills are essential for cyber security professionals. This skill includes knowledge of networking, operating systems, and software engineering. Familiarity with databases, scripting languages, and cyber threats is also beneficial.
- Communication Skills:
Students must communicate effectively with others. This skill includes being able to clearly explain technical concepts as well as interact professionally with clients.
- Computer Networking:
Students must be familiar with computer networking protocols, such as TCP/IP, Ethernet, and Wi-Fi. Students should also be comfortable configuring and troubleshooting networks.
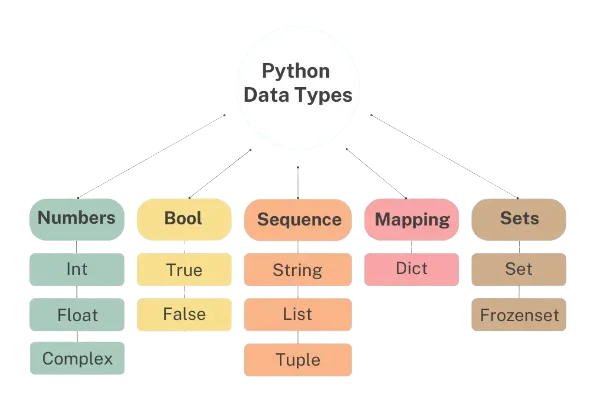
- Programming:
Students should know at least one programming language, C, Java, or Python. Cyber Security Course fee, A basic understanding of object-oriented programming, data structures, and algorithms is also recommended.
- Problem-Solving Skills:
Aspiring students must identify and solve problems quickly and effectively. This skill requires analytical thinking and the ability to troubleshoot technical issues.
Cyber Security Course Fee After 12th
The top cyber security courses after the 12th are
- BTech Cyber Security
- BSc Cyber Security
- MTech Cyber Security
- MSc Cyber Security
Cyber Security Course Fee After 12th: Eligibility,
Cyber Security courses are available to students after the 12th Grade with different eligibility criteria depending on the type and level of the course.
The types of Cyber Security course fees available after 12th Grade:
Program | Eligibility |
BTech Cyber Security | Candidates should secure at least 50% marks in classes 10 & 12 with physics, chemistry, and math as core subjects. They should also qualify for JEE Main/State or University level engineering exams. |
BSc (Hons) Cyber Security | Candidates must pass the 10+2 exam with math as one of the core subjects. They should score more than 50% marks in 10+2. |
MTech in Cyber Security | Candidates should possess BTech/BSc/CS/IT/MA degree from a recognised university and secure 50 – 60% marks. They should also qualify for the GATE exam and appear for the interview. |
MSc Cyber Security | Candidates should possess BE/BTech/BArch/BCA/CS/IT degrees from a recognised university. They should secure at least 50 – 55% marks and opt for statistics or mathematics as core subjects. |
Top Cyber Security Course Fee Colleges in India
Some of the Cyber Security Course Fees are high. However, that is pure because of the quality that the institute provides.
College | Course | fee |
Ramaiah Institute of Technology | BTech in Computer Science and Engineering (Cyber Security) | INR 8,88,000 |
PES University | MTech in Computer Science and Engineering | INR 5,01,000 |
Executive MTech in Cyber Security and Engineering | INR 12,01,000 | |
Shaheed Sukhdev College of Business Studies | PG Diploma in Cyber Security and Law | INR 75,400 |
K.K. Modi International Institute | MSc in Cyber Security | INR 64,000 |
Ganga Institute of Technology and Management | MTech in Cyber Forensics and Information Security | INR 1,54,000 |
Ramrao Adik Institute of Technology | BTech Information Technology (Cyber Security and Digital Forensics) | INR 58,000 |
IMS Proschool, Andheri West | Post Graduate Program in Cyber Security in association with CompTIA | INR 15,000 |
Certificate in Cyber Security | INR 15,000 | |
TMV – Tilak Maharashtra Vidyapeeth | Post Graduation Diploma in Cyber Security (PGDCS) | INR 43,200 |
IMS ProSchool, Pune | Online Certificate in Cyber Security | INR 1,55,000 |
Amity University Online | Online Diploma in Cyber Security | INR 1,85,000 |
Praxis Business School | PGP in Cyber Security | INR 3,59,000 |
Techno India University | BTech in Computer Science and Engineering (Cyber Security ) | INR 6,32,000 |
Conclusion
All of the above courses are highly suitable for aspirants looking for a career in cyber security or to learn more about that. Some of the Cyber Security Course Fees are high. However, that is pure because of the quality that the institute provides. Everyone also benefits from the work of cyber threat researchers, like the team of 250 threat researchers at Talos, who investigate new and emerging threats and cyber attack strategies. They reveal new vulnerabilities, educate the public on the importance of cybersecurity, and strengthen open-source tools. Their work makes the Internet safer for everyone.
Frequently Asked Questions
How much does IT cost to be a cyber security?
Many cybersecurity associate degree programs offer flexible learning schedules. This is ideal for students with other commitments. The cost of an associate degree in cybersecurity ranges from around $7,000 to nearly $20,000, depending on whether you study in or out of state and whether your school is public or private.
Is the cyber security course fee expensive?
Cybersecurity is quite a lucrative industry to begin your career. The Cyber Security Course fee for cyber security can range from 30,000 to 1,50,000 INR in line with the level of training and the institute you opt to attend.
Is cyber security easy for beginners?
Learning cybersecurity can be challenging, but it doesn’t have to be difficult, especially if you’re passionate about technology. Nurture a curiosity for the technologies you’re working with, and challenging skills become more manageable.
Should I study cyber security?
Some of the Cyber Security Course Fees are high. However, that is pure because of the quality that the institute provides. The whole point of cyber security is to protect companies from potential threats, which in itself makes you a hero day after day. However, preventing or solving a major cyber crime can be rewarding and help add excitement and recognition to your career.